2-factor authentication services
Updated: August 01, 2023
Two-factor authentication (2FA) is a security mechanism that adds an extra layer of protection to user accounts and systems by requiring two different forms of identification before granting access. Typically, this involves something the user knows, such as a password or PIN, and something the user possesses, like a smartphone or hardware token. When logging in, the user must provide both pieces of information to verify their identity, significantly increasing the security of the authentication process. 2FA helps prevent unauthorized access, as even if a password is compromised, the additional factor provides an additional barrier for attackers. As cyber threats continue to evolve, 2-factor authentication has become a critical security measure for protecting sensitive data and maintaining the integrity of user accounts across various online platforms and systems.
See also: Top 10 Identity Management platforms
See also: Top 10 Identity Management platforms
2023. Google Authenticator can now sync 2FA codes to the cloud
Google Authenticator has been updated to enhance its usability for those who frequently utilize the service to log in to websites and apps. Starting today, Google Authenticator will synchronize any one-time two-factor authentication codes that it generates to users' Google Accounts. Prior to this update, these one-time codes were saved locally on a single device. As a result, losing the device meant losing access to any service set up with Authenticator's 2FA. By updating the Authenticator app, users can take advantage of the new synchronization feature. If they are signed in to a Google Account within the Authenticator app, their codes will be automatically saved and restored on any new device they use.
2020. Google finally fixed the worst thing about its Authenticator app
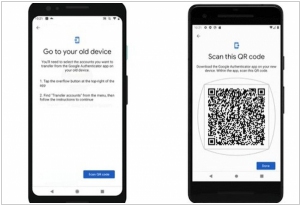
To enhance data security and protect against hackers, utilizing two-factor authentication is highly recommended, and Google Authenticator serves as a straightforward and sensible choice. Excitingly, a new feature has been added to Google Authenticator, making it effortless to transfer data from one phone to another. Google Authenticator is a mobile application that generates a dynamic, constantly changing code. This code, along with your password, is required to access various online accounts, including Facebook, Gmail, and Twitter. With the recent update, Google has introduced the capability to seamlessly transfer all data from Google Authenticator to a new phone. The process is straightforward, involving the selection of an account and scanning a QR code using the old phone.
2018. Cisco is buying 2-factor authentication provider Duo Security

Cisco has announced its acquisition of security firm Duo Security for a sum of $2.35 billion. This acquisition aligns well with Cisco's objectives, as Duo Security offers a security solution that enables employees to utilize their own devices for adaptive authentication. Instead of relying on traditional key fobs with security codes, Duo's technology ensures secure authentication on any device. Within the Cisco ecosystem, this solution seamlessly integrates and provides a natural fit for CTOs seeking robust two-factor authentication measures. In recent years, Cisco has strategically acquired several notable companies including OpenDNS, Sourcefire, Cloudlock, and now Duo Security.
2017. Okta makes 2-factor authentication standard for all customers
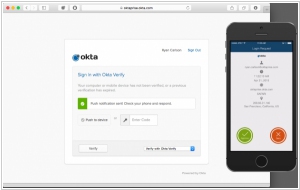
Cloud identity provider Okta has announced the implementation of two-factor authentication (2FA) as the standard security measure for all its customers. Research indicates that a significant number of data breaches stem from stolen or weak passwords. In response, Okta acknowledges this risk and aims to bolster security by introducing 2FA, which presents users with a unique one-time passcode. This additional layer of protection makes it more challenging for hackers to compromise accounts. Furthermore, Okta recognizes the issue of password reuse and has developed a compromised password detection tool. This tool scans widely-known data breaches to identify commonly-used passwords, enabling Okta to alert users if their passwords are at risk. While 2FA is not a foolproof solution, it offers an enhanced level of security beyond traditional username and password combinations. This initiative represents a significant stride towards reinforcing account protection.
2015. Authy makes 2-factor authentication as painless as possible
Authy, the startup specializing in two-factor authentication, has introduced its latest offering: the OneTouch authentication service. This innovative service aims to simplify the two-factor authentication process, making it remarkably convenient. Instead of manually entering a code generated on your phone into a web form, OneTouch utilizes a push notification system. When you attempt to sign in to a website, a push notification is sent to your phone, prompting you to confirm your intent to log in. By simply confirming the notification, you gain access to the site without the need for code entry. This streamlined approach significantly reduces friction typically associated with two-factor authentication. The underlying concept is that by entering the code on the website, you demonstrate that you have possession of the phone. Therefore, it makes sense to leverage the phone itself for authentication, taking the security process to the next level.
2015. Twilio acquires 2-factor authentication service Authy
Communications API provider Twilio has recently completed the acquisition of Authy, a service that offers two-factor authentication solutions to both end users and enterprises. Authy seamlessly aligns with Twilio, as Twilio has previously powered elements of the authentication and verification process for renowned brands like Intuit, Box, and GitHub. By integrating Authy's service into Twilio, users will benefit from an enhanced self-service and policy-management experience, along with features such as mobile phone-based TOTP (time-based one-time passwords). Interestingly, several Twilio customers have already developed their own two-factor authentication services utilizing Twilio's SMS and voice services. With the availability of Authy as a product option on Twilio.com, these customers will soon have the opportunity to streamline their authentication systems and migrate to Authy, following some necessary engineering adjustments.
2010. OneLogin - Single sign-on for SaaS apps

Thanks to SaaS technology, a large number of business applications have appeared. Now companies can use multiple applications from different vendors (not just from Microsoft). But along with the wide variety of applications the problems of their integration and a single sign-on have come. Various platforms, marketplaces and SaaS associations are intended to solve these problems: Force.com, Intuit Partner Program, Google Apps Marketplace. OneLogin also tries to solve the single sign-on problem in simple and ingenious way. It is the centrally-administered username / password database + browser plugin, which makes working with a large number of SaaS applications very convenient. ***